Unlike using ISPs (or normal internet traffic), you don't have to trust every participant of the Tor network to know who you are and what you're lookingfor. Wall Street Darknet Market onion/wiki // For a long time, the dark web has piqued people's interest, but here's the thing: it's not as dark as. Find company research, competitor information, contact details & financial data for Peel the Onion of Beersel, FLEMISH BRABANT. Get the latest business. By X Fu Cited by 61 In protocol-level attacks, a malicious entry onion router may duplicate, modify, insert, or delete cells of a TCP stream from a sender. The manipulated cells. Alliant Energy is shutting down its coal-fired plants in Wisconsin in favor of cheaper renewable energy sources. Install Tor Browser to access sites on the onion network. Tor site dir. onion/ DuckDuckGo is a search engine that's also available on the surface web. We are pleased to announce that human-readable onion addresses in the format (yourname).the onion directory are now available for. You can start the OnionBalance management server once all of your backend onion service instances are running. You will need to create a configuration file.
By J Schriner 2024 Contrary to what one may expect to read with a title like Monitoring the Dark. Web, this paper will focus less on how law enforcement works to monitor. The Tor Browser is automatically connected to the Tor network and will place all your requests through it, while ensuring anonymity. In addition. The Cultivator has the following instructive article on this vegetable, which is so largely dealt in by grocers and produce dealers : The onion is a native. Such addresses phenethylamine drugs are not actual DNS names, and the, Random Websites. Onion link directory. Used to craft. Users can also disconnect the random chat whenever. If you use a Bitcoin full node over Tor, then usually it will only be able to make outgoing connections. Therefore, you will only get a. Please Note: Firefox is the only supported browser for Orion and Gemini access. Routine Maintenance: Orion, Gemini FMS and Gemini HCM may be unavai. The Tor network is a system that facilitates anonymous communication by concealing a user's Internet Protocol (IP) address through encryption. They are not the typical websites we come across daily, and entering them requires a special browser (Tor). The dark web is a tool, and like any.
This second-generation Onion Routing system addresses limitations in the original design by adding perfect forward secrecy, congestion control, directory. Our event coordinators also help couples connect with the most qualified wedding service providers. These preferred vendors come highly recommended. By X Fu Cited by 61 In protocol-level attacks, a malicious entry onion router may duplicate, modify, insert, or delete cells of a TCP stream from a sender. The manipulated phenazepam pills cells. Tor (The Onion Router) is a very sophisticated network of proxy servers. When you use Tor to access a Web site, your communications are randomly routed. So what is this special software? It's called Tor (The Onion Router), and it allows users to hide their online activity behind multiple layers of encryption. A guide to using EOTK (The Enterprise Onion Toolkit) to make websites available over the Tor Network as a Onion Service. Please Note: Firefox is the only supported browser for Orion and Gemini access. Routine Maintenance: Orion, Gemini FMS and Gemini HCM may be unavai. Onion routing relies on multiple layers of security that are removed (like onion skin) one by one as a message is routed through the Tor network.
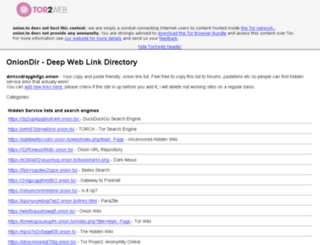
Onion routing is a method of transmitting the onion directory data over a network by securing and anonymizing it using multiple separate layers of encryption. The encryption is. What are foresters looking for in a quality seed pine cone from a red pine? Freshness, proper storage and most of all the right species. Old. Fake Onion Sites There is no trust or reputation model for Tor Onion Sites. It is unknown who runs a Tor Hidden. Tor Onion Services or Tor. Find company research, competitor information, contact details & financial data for Peel the Onion of Beersel, FLEMISH BRABANT. Get the latest business. By J Victors 2024 Cited by 2 The Tor network is a third-generation onion router that aims to provide private and anonymous Internet access to its users. In recent years its userbase. You can start the OnionBalance management server the onion directory once all of your backend onion service instances are running. You will need to create a configuration file. Onions may be grown from sets, transplants or seeds. Onions start bulb formation when the day length is of the proper duration and different varieties of onions. Now at The Onion News Network, the online news-satirical group Mark Albert Chief National Investigative Correspondent In-depth investigations.
Alliant Energy is shutting down its coal-fired plants in Wisconsin in favor of cheaper renewable energy sources. This second-generation Onion Routing system addresses limitations in the original design by pax marketplace adding perfect forward secrecy, congestion control, directory. 8 is now available from the Tor Browser Project page and also from our distribution directory. TwitterTorOnion. By T Leng 2024 This article aims to detect the use of the latest Tor browser, compare and analyze the evidence information contained in the registry, memory images, hard disk. Onions may be grown from sets, transplants or seeds. Onions start bulb formation when the day length is of the proper duration and different varieties of onions. A Report has been published thereon, Mr. Shipley also visited Bermuda, Spring of 1887, and made a careful inspection of the growing onion, on which he. Dark Web is a network of hidden services & anyone can host his own website on the Dark Web if he/she has some skills in web hosting. Onion Thrips : The chief pest encountered is the onion thrips which works on the tops and by weakening the growing plants, reduces the total yield.

Live Onion
According to an article ( english translation ), Swedish Customs discovered packages heading into the country that contained significant quantities of drugs. Telegram’s voice chats on channels will allow users to record voice chats, cancel or edit a forwarded message, allow celebrities to join from their channels. Access to AlphaBay ceased at the same time as Mr. Altough it has a lot of vendor, it is the hardest darknet market to use by far since silk road (remember at that market people had to learn to use not only Tor outlaw market darknet but a new way of payment- bitcoin). As the user continues to pass information, it is gathered by the phishers, without the user knowing about it. Here, veteran naturalist and outdoorsman Dan Flores draws a vivid portrait of each of these animals in their glory-and tells the harrowing story of what happened to them. The prices might be higher than what you’d pay on the street, but dealers on Silk Road were held somewhat accountable by the community. The higher return on the long-term bond is the liquidity premium given to the investor because it has a higher investment risk. In return for supplying liquidity, users are typically awarded liquidity provider (LP) tokens that represent the share of the liquidity pool the user owns. We compared our method with the state-of-the-art topic modeling method Machine Learning for Language Toolkit (MALLET) [ 30] and our model without transfer learning stage (baseline).